Exploring User and Provider Management in VAST Data VMS
User and provider management in VAST Data VMS represents a critical component of the system’s security architecture. The Virtual Management System (VMS) uses Role-Based Access Control (RBAC) to provide granular permissions across different administrative realms, allowing organizations to enforce the principle of least privilege while simplifying management of user access.
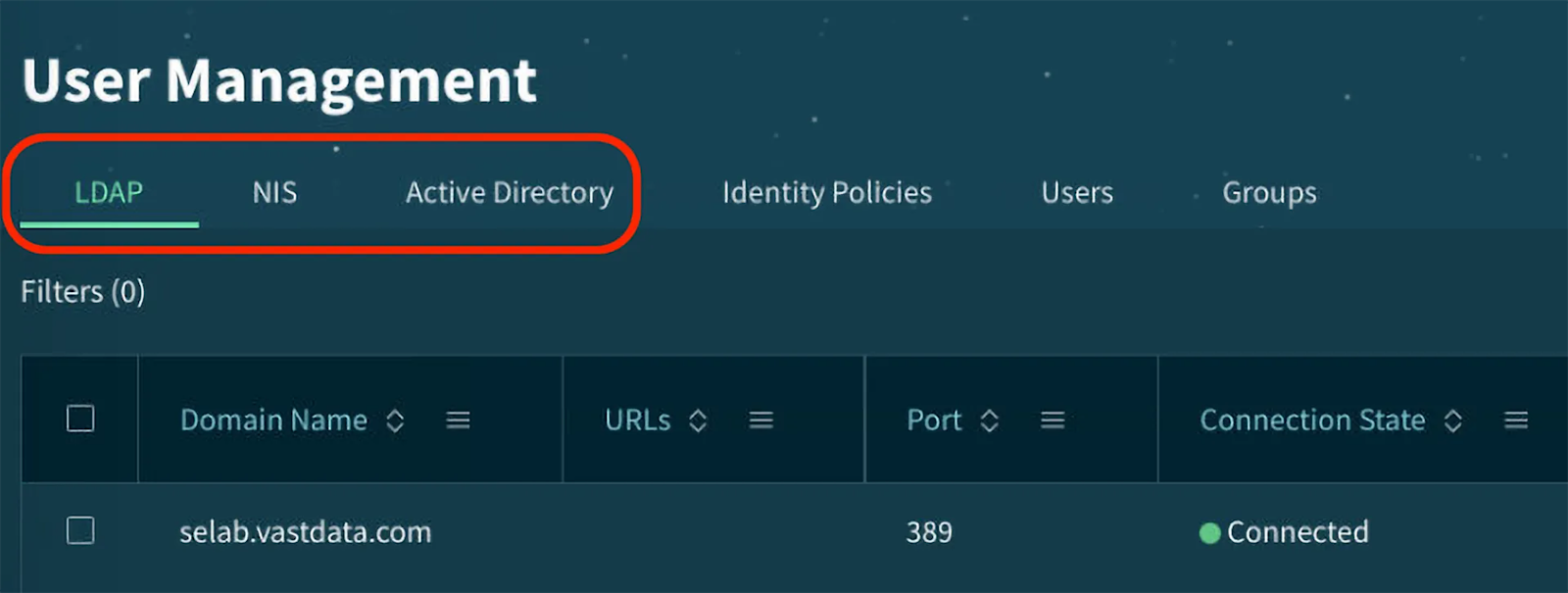
In this lab, we’ll explore how VAST handles user identities, authentication, and authorization through various identity providers, including Active Directory, LDAP, NIS, and local users. We’ll understand how these components work together to create a unified access management system across all protocols supported by VAST.
Prerequisites
Before beginning this lab, please ensure you have a Cosmos Community account, as it’s needed to proceed and access the lab environment.
Access the VAST Management System GUI
Access The VAST Data Lab Environment
Go to this URL vastdata.thecosmoslabs.com or click the button below:
Make sure you’re logged in with your Cosmos community account.
VAST Data lab environment login page
Click “Launch Lab Environment”. You might need to allow popups for the site, so if nothing happens, make sure you do so.
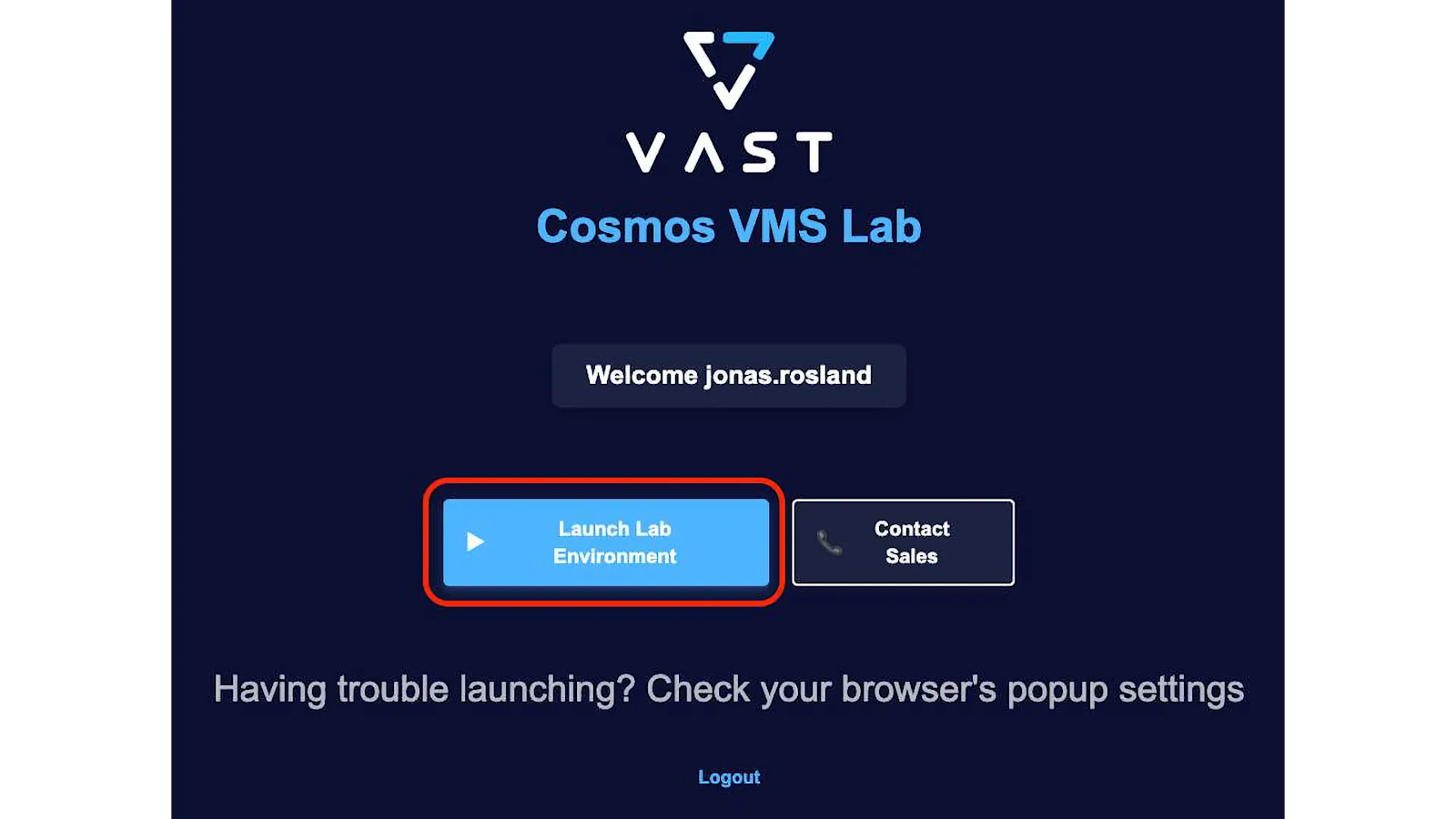
Upon entering the lab environment, click to accept the end user agreement.
At the login screen use the credentials provided.

Exploring Role-Based Access Control (RBAC)
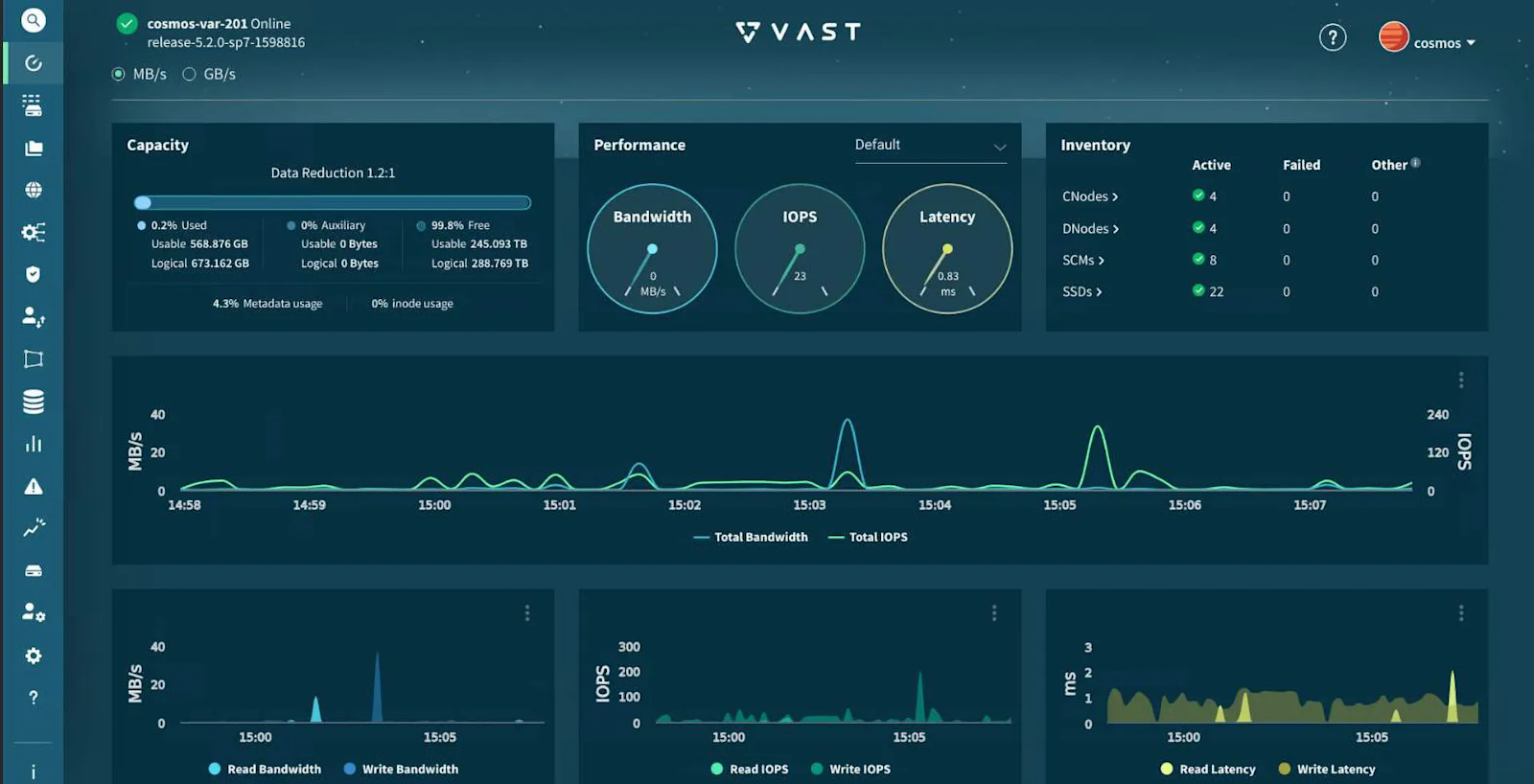
You will start off in the Dashboard section of the VAST Management System GUI. This section provides an overview of the system’s health and performance.
The left-hand navigation will open other sections in the GUI. For a full list of sections, click here.
Note that we’re operating in read-only mode, so we’ll focus on observing rather than modifying.
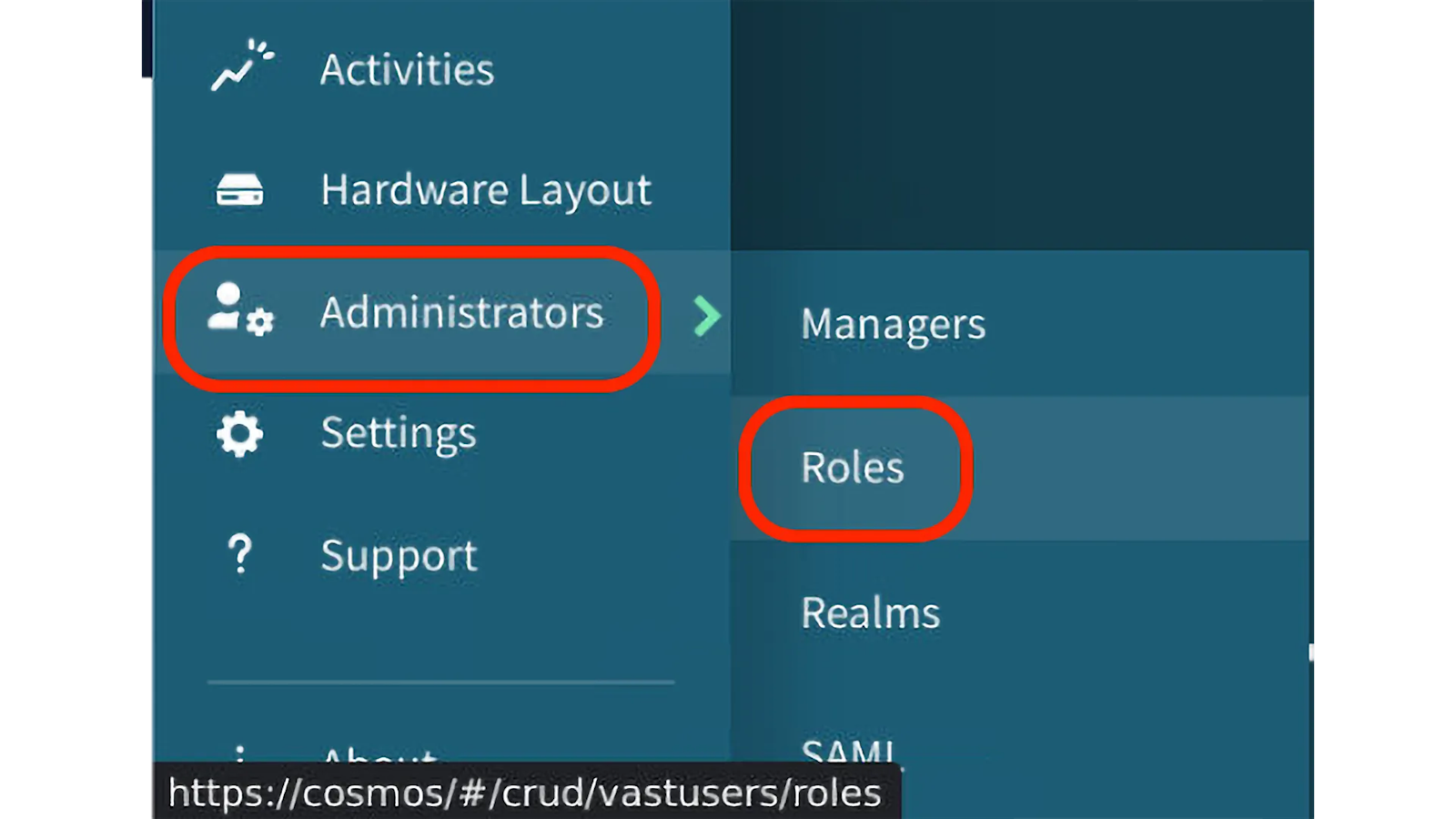
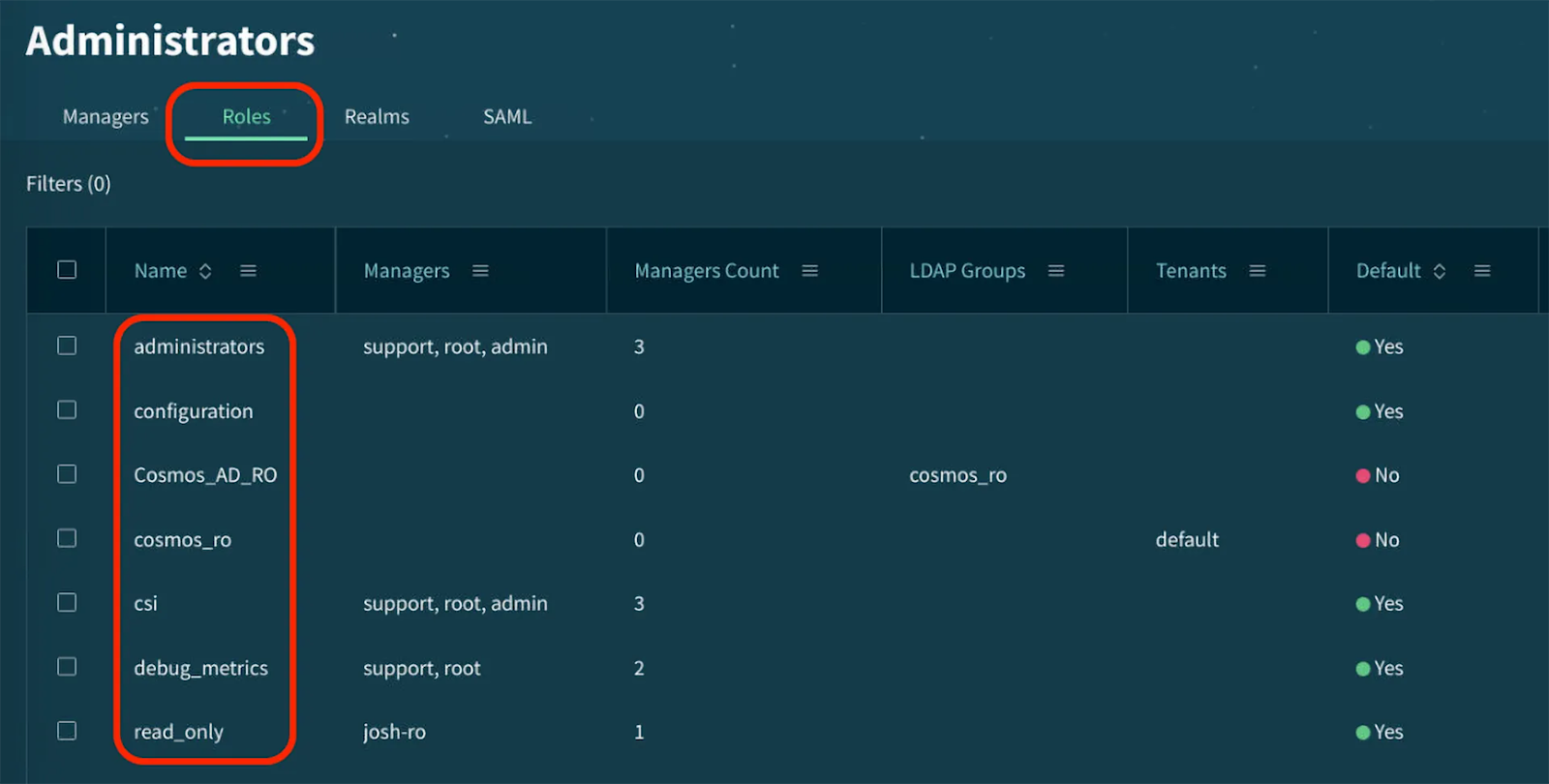
1. Navigate to the Roles section
From the main navigation menu to your left, go to the “Administrators” section close to the bottom
Select “Roles” to view the available roles in the system
You’ll see a list of all defined roles with their names and brief descriptions
2. Examine Predefined Roles
VAST comes with several built-in roles that serve specific administrative purposes, such as:
Administrators: This role grants comprehensive access to all realms and functions, allowing users to perform any action within the system. It’s typically reserved for senior IT staff responsible for overall system management
Read Only: This role provides view-only access across all realms, allowing users to monitor the system without making changes. It’s ideal for junior administrators, auditors, or monitoring staff.
Configuration: This specialized role focuses on system configuration tasks, with appropriate permissions to set up and modify system parameters.
CSI: This role is designed specifically for Container Storage Interface operations, granting the necessary permissions for Kubernetes integration.
debug_metrics: This technical role provides access to detailed system metrics for debugging purposes.
Notice these predefined roles cannot be modified—this restriction ensures system stability and security.
3. Understand Role Structures and Realms
On each role, click on the ☰ button to your right to View and examine its specific permissions across different realms.
The permission matrix is organized by administrative realms, which represent functional areas of the system:
Events Realm: This realm governs all event management functions, including: • Creating, viewing, and managing system alerts Setting up event triggers and responses
Hardware Realm: This realm controls access to physical component management: • Monitoring CNodes (compute nodes) status and performance • Managing DNodes (data nodes) configurations • Implementing hardware upgrades or replacements
Logical Realm: This critical realm manages the logical storage structure: • Creating and managing views • Setting quotas to control storage usage • Configuring network access settings such as virtual IPs and protocols
Monitoring Realm: This realm focuses on system health and performance: • Accessing real-time performance metrics • Viewing historical performance data • Setting up monitoring dashboards
Security Realm: This realm controls access to security functions: • Managing user authentication methods including external identity providers • Setting up encryption policies • Managing the RBAC system itself
Settings Realm: This realm handles general system configurations: • Setting system-wide parameters • Managing licensing information
Support Realm: This realm provides access to support functions: • Generating support bundles for troubleshooting • Accessing system logs and diagnostic information • Managing firmware and software updates • Configuring remote support access
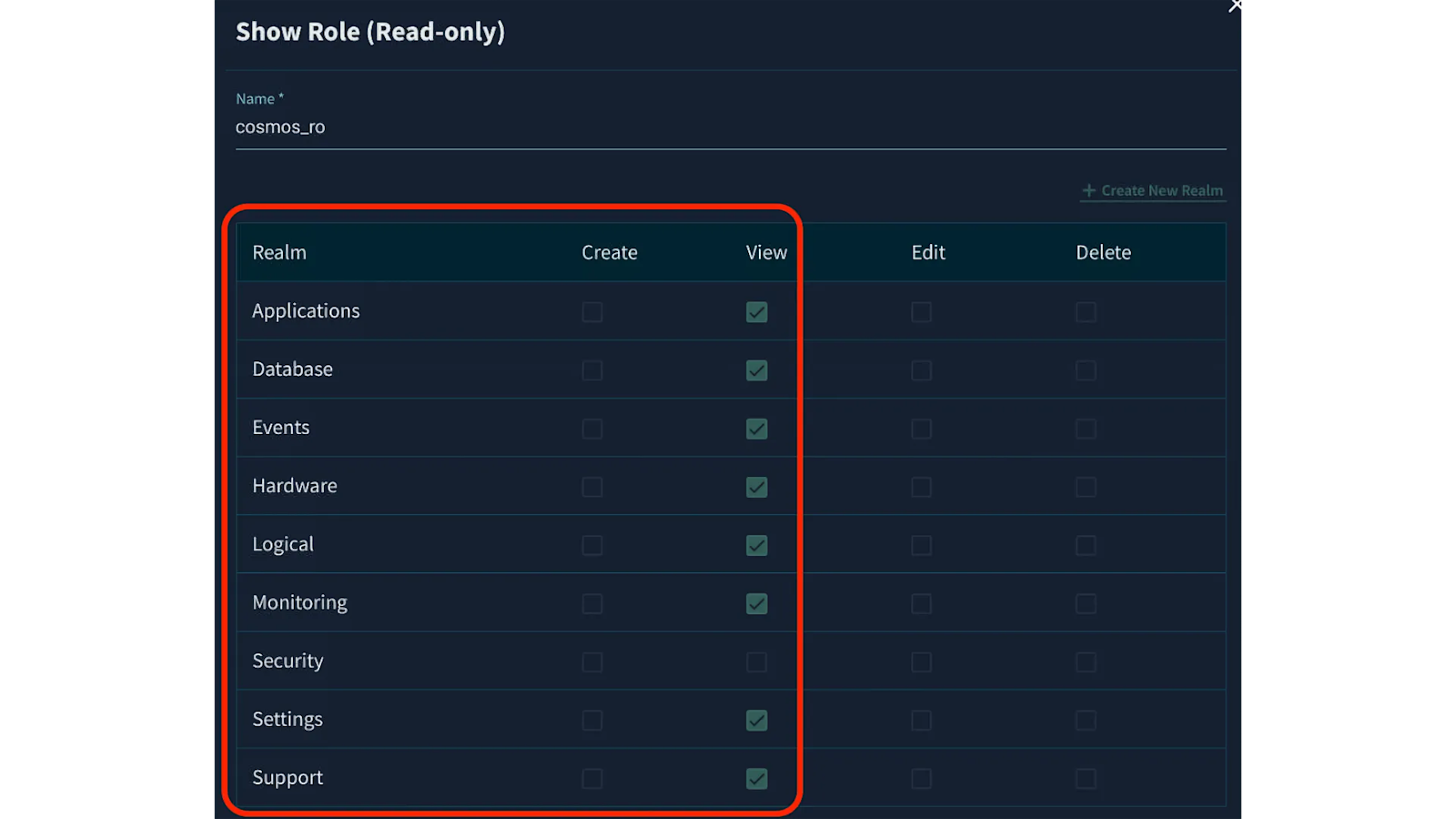
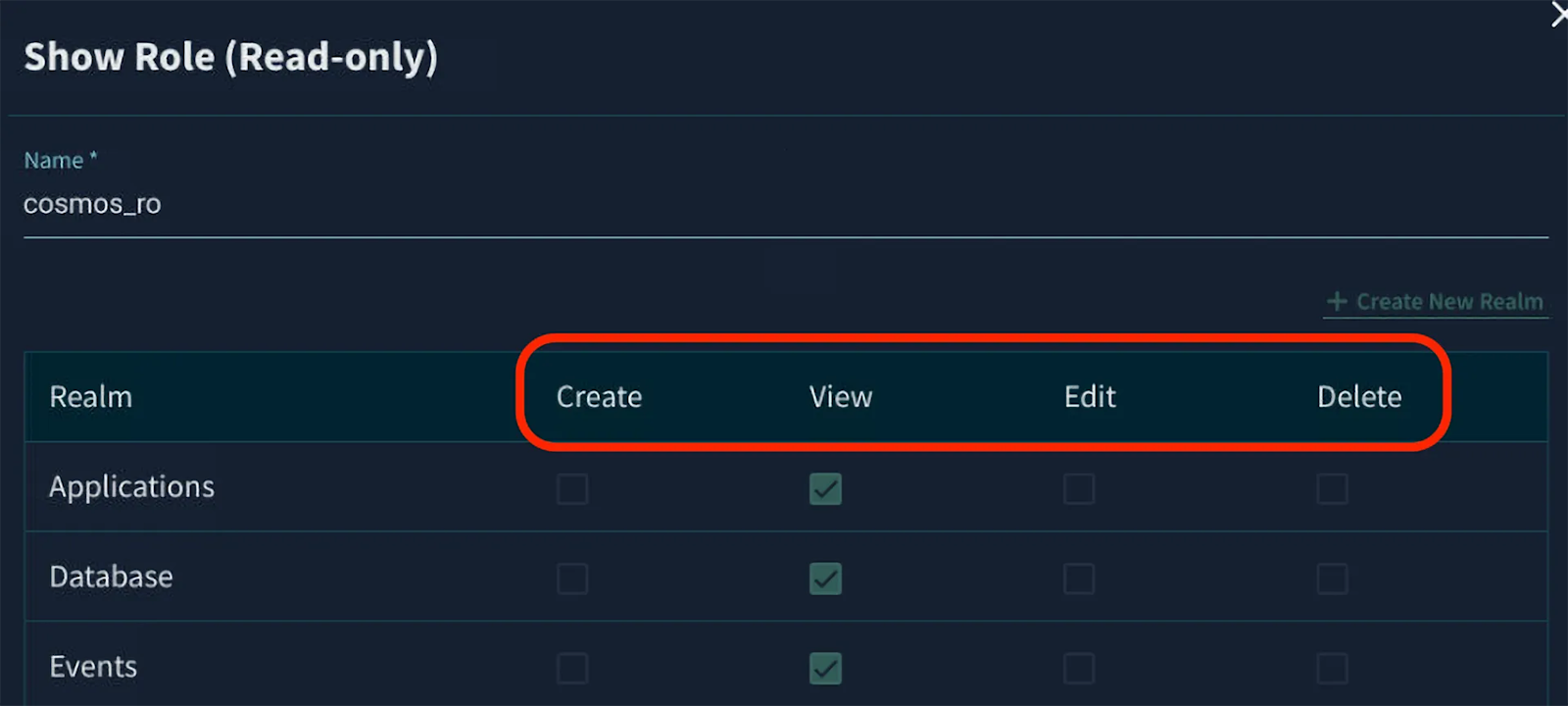
4. Explore Permission Types
For each realm, examine the four fundamental permission types that can be granted:
Create: This permission allows users to add new resources or configurations within a realm. For example, in the Logical realm, Create permission would allow adding new views or quotas.
View: This basic permission lets users see resources without modifying them. It's the foundation of read-only access and is often granted broadly for monitoring purposes.
Edit: This permission enables users to modify existing resources but not create new ones. For instance, Edit permission in the Hardware realm would allow reconfiguring existing nodes but not adding new ones.
Delete: This powerful permission allows users to remove resources from the system. It's typically restricted to prevent accidental data loss.
Notice how permissions can be combined to create precise access profiles:
Some roles might have View-only access to sensitive realms like Security while having full permissions in other areas
Other roles might have Create and Edit permissions but not Delete, limiting potential damage from accidental actions
Observe how clicking on column or row headers can toggle all permissions in that column or row, simplifying role configuration.
5. Understand Role Assignment Logic
Take note of how user permissions are calculated:
Users inherit all permissions from all roles assigned to them
If a user has multiple roles with conflicting permissions, the most permissive access is granted
For example, if one role grants View access to a realm and another grants Edit access, the user will effectively have Edit access
This inheritance model simplifies administration but requires careful role design to maintain security,
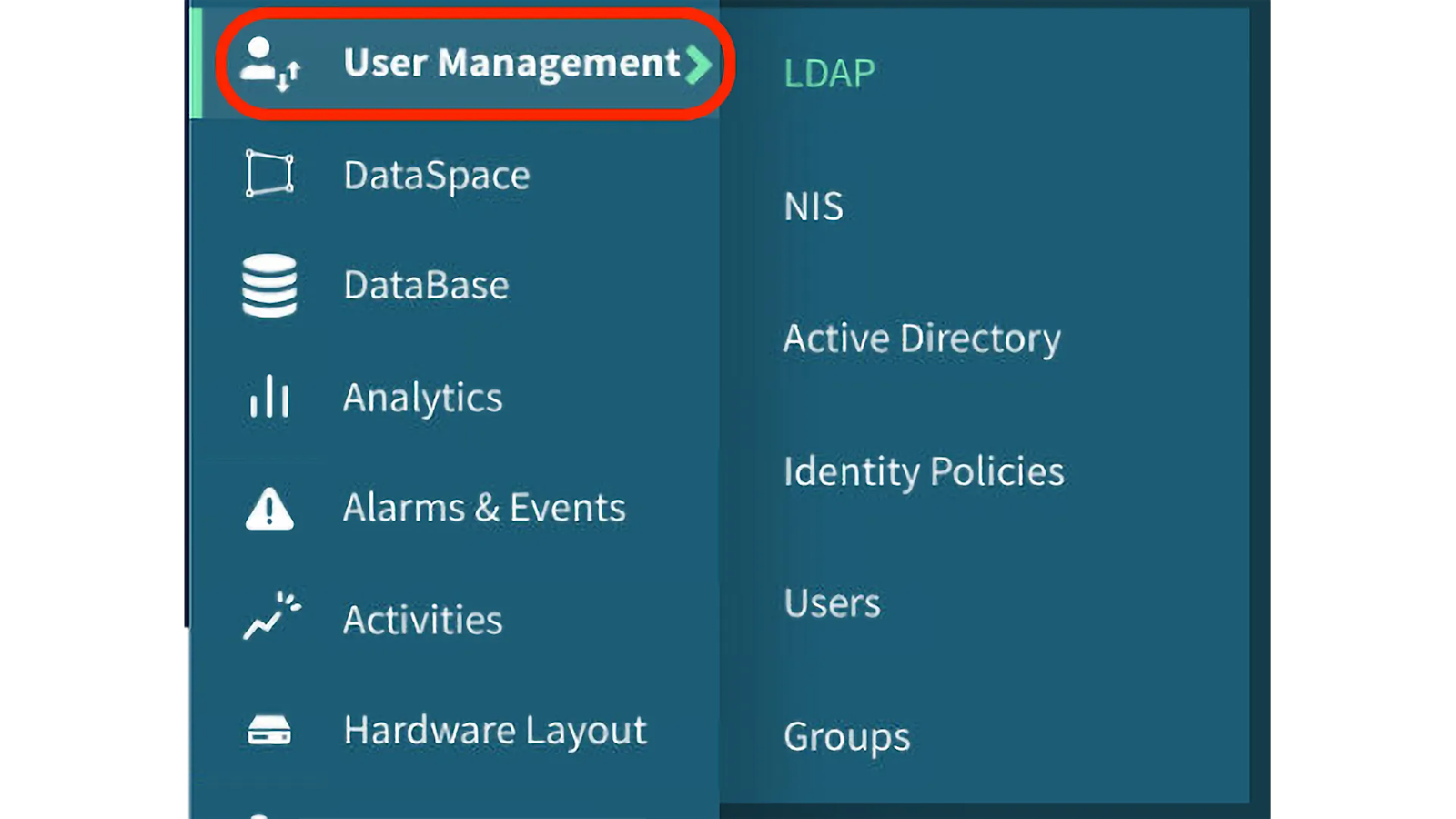
6. User Management
Navigate to the User Management Section.
Observe the list of configured identity providers, which may include:
Active Directory: Microsoft’s enterprise directory service
LDAP: Lightweight Directory Access Protocol services
NIS: Network Information Service (legacy Unix directory)
Users: Local users defined directly within VAST
Note that VAST supports using multiple providers simultaneously, creating a flexible authentication framework.
This multi-provider approach allows organizations to leverage existing identity infrastructure while maintaining specialized access for system management.
External Identity Providers
VAST employs a sophisticated process called “stitching” to create unified user identities. When a user connects to the system, VAST queries all configured providers. If the user exists in multiple providers, VAST combines (or “stitches”) their attributes. This creates a single coherent identity with consolidated permissions and attributes.
This stitching mechanism provides several benefits:
Users maintain consistent identities regardless of access protocol (NFS, SMB, S3)
Administrators can leverage existing directory services without duplication
The system presents a unified view of users despite diverse backend sources
Key Takeaways
Effective RBAC Implementation • VAST’s RBAC system organizes permissions by functional realms, allowing administrators to grant precise access based on job responsibilities • Roles serve as permission containers that can be assigned to users, simplifying administration • The principle of least privilege is enforced by granting users only the necessary permissions for their tasks • The combination of multiple roles provides flexible access management that can adapt to complex organizational structures
Unified Identity Management • VAST supports multiple identity providers simultaneously, including Active Directory, LDAP, NIS, and local users • The “stitching” process combines user information from different providers, ensuring consistent identity across all protocols • This unified approach streamlines user management and enhances security • Protocol-agnostic identity management ensures consistent access regardless of how users connect to the system
External Provider Integration • VAST systems can join Active Directory domains for seamless integration with existing infrastructure • LDAP configuration allows organizations to leverage existing identity directories • Secure communication is ensured through encryption options like StartTLS and LDAPS • Attribute mapping provides flexible integration with various directory schemas and organizational structures
Local User Administration • Local VMS users can provide administrative access without relying on external providers • This is particularly valuable in environments with limited external connectivity • Local users can be assigned specific roles based on their responsibilities • Regular password management is essential for maintaining security • A comprehensive user lifecycle management approach should be used to support security and compliance requirements
Centralized Access Control • VAST’s user and provider management system offers centralized control over authentication and authorization • This centralized approach enhances security, simplifies administration, and supports compliance requirements • Administrators can efficiently manage user access across the entire VAST platform • The combination of external and local user management provides flexibility and resilience
By understanding these concepts and practices, you’ll be able to implement effective user and provider management in your own VAST environment, ensuring security while simplifying administration.